Bellingcat: how one man’s digital-sleuthing hobby exposed the Salisbury poisoners
On 8th October 2018 the second suspect in the poisoning of the Skripals in Salisbury was identified as a member of Russian military intelligence. The breakthrough wasn’t made by British security services, but by an investigation website started by a former lingerie-industry employee. In DG #33 we met Eliot Higgins, founder of Bellingcat, the open-investigation site that grew from “a bit of intellectual stimulation” to a formidable intel hub taking on the world’s rogue actors

Illustrations: Angus Greig
8th October 2018 (Taken from: #33)
For a man trying to reassure me about his personal safety, Eliot Higgins is doing a terrible job. “There’s this sort of GoFundMe for jihadis on the dark web,” he tells me, having just insisted he is not worried about threats against his life. “Extremists post about an attack they’re planning and supporters donate to fund them to carry it out.”
Higgins discovered this Kickstarter for terror in an unlikely fashion. Apparently angered by the work he has done exposing terror cells, many of the fundraisers had geotagged the offices of Bellingcat, the investigative website he runs, as their location when using the website. “The first I knew about it was when counter-terrorism police knocked on the door and I had to explain I wasn’t planning a string of atrocities, that it was just some jihadis’ idea of a joke,” says Higgins.
Fundraising Islamists are just one group who are not fans of Higgins and Bellingcat’s brand of open-source investigation. Since its creation five years ago, the site – which has the tagline “By and for citizen investigative journalists” – has used evidence found online, including social media posts, YouTube videos and leaked databases, to expose the wrongdoings of some of the most feared forces on the planet including Iraqi war criminals, Mexican drug lords and the Syrian army.
One alias was linked to another… We were peeling through layers of fake identities – they were like Russian dolls”
In truth, if a disgruntled extremist were to strike Bellingcat’s office on a leafy side street in Leicester, the only thing they’re likely to destroy is some unopened post. As sparse as a monk’s cell, the single room contains little more than a desk, a microphone and a wastepaper bin filled with some of the letters from conspiracy theorists that Higgins regularly receives. Higgins, 40, explains that he spends very little time here, preferring – as do the rest of his network of investigators – to work remotely, using his laptop to tap in to the far reaches of the internet and uncover the information he seeks.
The results of Higgins’s online sleuthing have been extraordinary. Since 2012, when he began blogging under the pseudonym Brown Moses, he has set out to find needles in the densest of virtual haystacks. His work has linked the 2013 chemical attack in Ghouta, Syria, to troops fighting in support of Bashar al-Assad’s regime; discovered the possible location of American journalist James Foley’s execution by Islamic State forces; identified the missiles used in a Saudi-led attack on a wedding in Yemen as those of an American arms manufacturer; and attributed the downing of Malaysian Airlines Flight MH17 to Russian forces.
The latest claims hauled up by Bellingcat’s digital dragnet could be the most explosive to date. In autumn 2018 the site identified the suspects in the poisoning of former spy Sergei Skripal and his daughter Yulia in Salisbury that March as members of Russian military intelligence agency the GRU – an assertion made in direct contradiction of President Putin’s claim that the two were merely civilians on a sightseeing trip.
Although Russia’s involvement had long been suspected, the fact that the link was discovered by civilians rather than the British security services sent shockwaves across the world. “It was incredible,” says Higgins of the moment his team made the connection. “We found one fake name linked to another alias, linked to another. We were peeling through layers of fake identities – they were like Russian dolls.”
Belling the cat
Bellingcat’s very existence is unlikely. Having studied media technology at Southampton Institute for Higher Education in the late ’90s, Higgins found the old-school approaches he was being taught to be out of step with the digital revolution he was witnessing. He dropped out, taking a string of IT admin jobs and immersing himself in the gaming world.

Eliot Higgins, founder group Bellingcat. Photo: Tolga Akmen / AFP / Getty Images
That changed with the birth of his daughter in 2012. “I used to like playing games, but then you don’t really have much of a chance to do that when you’ve got a six-month-old,” he says. “So I thought I could do with a hobby that I can pick up and put down really easily.” But rather than taking up stamp-collecting or scrapbooking, he started investigating mass atrocities through evidence he found online and publishing the results on his blog. “It was just a bit of intellectual stimulation,” he says.
That blog, Brown Moses, named after a song by Frank Zappa, soon started gaining recognition and Higgins began exploring options to turn his hobby into his livelihood. “I seemed to be finding information no one else was finding, but I couldn’t figure out how I could get a job doing it professionally,” he says. “I applied for journalist training courses at the BBC and ITV and I was turned down by both. I didn’t make it past the first round.” He smiles. “Next week I’m booked to train both organisations – funny how it works out.”
With mainstream journalism’s doors apparently closed and with his contract doing IT administration for a women’s lingerie manufacturer soon to expire, Higgins was preparing to call time on his digital sleuthing. “A big scoop I had uncovered about Croatian weapons being smuggled into Syria was on the New York Times front page, but I couldn’t make ends meet,” he says.
“I was offered a job by a private intelligence company, but it meant I would have to stop the blog. When I posted the news, people started saying, ‘Well, what if we fund it?’ So I took a gamble on crowdfunding. It was literally a case of, ‘If I don’t hit this figure, I’m not going to be able to pay my mortgage.’ Looking back, it was a very stupid idea, but sometimes the best ideas are the most stupid.”
Having made enough to keep a roof over his family’s head, Higgins continued to publish data-driven scoops as Brown Moses until 2014. By then he had realised there were more and more open-source investigators without a platform and he felt a need to inspire the next generation. “So I thought, ‘I’ll launch a new site,’” he says. “One half would be investigations and the other half was going to be guided case studies to get people to learn how to do it for themselves.” He named the new site Bellingcat after the Aesop fable about a group of mice who decide to place a bell around their feline nemesis’s neck to warn them when it was nearby. “They didn’t actually have a plan for how to do it,” smiles Higgins. “They just had the idea. And I thought, ‘That sounds about right.’”
Location, location, location
Bellingcat went live on 14th July 2014, mixing investigations with how-to guides including ‘Verification and Geolocation Tricks and Tips with Google Earth’ and ‘Tankspotting: How to Identify the T-72B3’. Three days later, Flight MH17 from Amsterdam to Kuala Lumpur was shot down over Ukraine, killing all 283 passengers onboard and 15 crew members. Russian military officials claimed the flight was hit by an air-to-air missile fired by a Ukrainian fighter pilot. They presented a host of evidence to support such claims – including radar data they said showed fighter jets in the vicinity of the Boeing 777, testimony from a Kiev-based Spanish air-traffic controller that stated that two Ukrainian fighter jets followed the Malaysian plane and satellite images of an aircraft firing on the airliner. Bellingcat smelled a rat.
Over the following months Higgins and his investigators dismantled Russia’s official line: the radar data was revealed to show debris from the destroyed passenger plane rather than jet fighters; the Spanish embassy confirmed that there was no air-traffic controller from Spain at either of Kiev’s airports; and the ‘satellite images’ were shown to be a selection of pictures found on Google and Photoshopped together.
Some people think they’re indestructible when they’re posting stuff online. It’s great for us”
The site followed this series of scoops with the publication of a 35-page report which used online data from sources including social media, Google Earth and Google Maps to link a Buk missile launcher operated by the 53rd Anti-Aircraft Rocket Brigade in Kursk, Russia, to the downing of the flight. The same conclusion was later reached by the Dutch-led international Joint Investigation Team. In May 2018, Dutch foreign minister Stef Blok said that “the government is now taking the next step by formally holding Russia accountable” for a breach of international law, while admitting that it would involve “a complex legal process”.
Russia responded to Bellingcat’s work with outrage. “In the absence of any trustworthy proofs that ‘Russians did it’ the Dutch investigators started to rely more and more on social media and on the findings of investigator groups like Bellingcat,” wrote Dmitry Polyanskiy, Russia’s first deputy permanent representative to the United Nations, in an open letter published in August 2018. “We also have a lot of reasons not to trust particularly Bellingcat, which was repeatedly caught red-handed by internet users by voicing anti-Russian or anti-Syrian allegations based on fakes. And these fakes are largely exposed in the web.”
Higgins isn’t worried. “We’ve been attacked by the Russian state for years, saying we’re working for the deep establishment in the UK and all kinds of nonsense like that,” he says. “In a way, it’s good for us because it raises our profile. Generally, anyone who’s going to believe Russia is going to believe them and anyone who isn’t will think, ‘They’re being attacked. They must be doing something right again.’”
Polyanskiy’s letter did touch on a criticism often levelled against Bellingcat online: that its funding influences its reporting. “Internet users have a lot of questions about Bellingcat financing,” the Russian wrote. “Important American and Western funds that traditionally support anti-Russian campaigns are said to be the main sponsors of these ‘investigators’, which casts obvious doubt on their impartiality.”
On someone else’s Instagram account, you could see him with the mask pulled up and it was tagged with his real name”
“We get loads of stick from people on the internet for our sources of funding; it’s just very tedious,” says Higgins, who explains that 50 percent of the site’s income now comes from donors including Google Digital News Initiative and billionaire George Soros’s grant-making institution, the Open Society Foundation.
“The funding doesn’t influence our work. If someone came to us and said, ‘I’m going to give you this amount of money and you have to write these things,’ I would immediately write a Bellingcat post exposing them.”
The other half of the site’s funding comes from the Bellingcat team’s work teaching open-investigation workshops around the world, which has in turn provided inspiration for fresh investigations.
“We were holding this workshop in London and one of our investigators got mugged by a moped gang,” Higgins says. “We had no idea this was a thing, so the entire class became an exercise in unmasking them through social media. By the end of the day we’d found out quite a lot of information about who [the moped gang] were, their names, where they hung out.
“There was one photo of a guy with a mask on, holding a wad of money, waving at the camera. On someone else’s Instagram account, you could see him with the mask pulled up and it was tagged with his real name. Some people really do seem to think they’re indestructible when they’re posting stuff online… It’s great for us because it just gives us another avenue to explore.”
The digital paper trail
Higgins didn’t need to trawl through social media accounts to find footage of the two men accused of deploying the Novichok nerve agent that poisoned five people in Salisbury and killed one of them, 44 year old Dawn Sturgess. They were right there, being interviewed on Russian state TV.

In an extraordinary interview on the state-funded RT network, broadcast on 13th September 2018, two men identifying themselves as Ruslan Boshirov and Alexander Petrov, whom the British police had named as suspects in the attack, said they had come forward to clear their names. Over 25 minutes they gave Wikipedia-quoting details of a two-day tourist trip to the UK, insisting they had visited the “wonderful” English city of Salisbury to see the cathedral “famous for its 123-metre spire”.
“We already knew there was something suspicious about these guys, but when they gave that ridiculous interview it just seemed completely absurd,” says Higgins. The Bellingcat team had already spent months trying to identify the suspects, working with the independent Russian news website The Insider. They would succeed in their efforts just two weeks after the broadcast. Their investigation started with the passport information released by the British authorities, which they traced to the original passport application form – a document Higgins describes as “really dodgy”, claiming it was filed at “this particular Moscow processing centre that’s only used for GRU agents and celebrities”.
Having found the GRU lead, the team’s major breakthrough came thanks to car-registration details. “We discovered there was a group of GRU officers who all registered their cars at the same building, the St Petersburg GRU headquarters,” says Higgins. “Because when they got pulled over and someone ran their plates, it would come up with that address, and they could get away with anything they wanted to.” By searching for cars registered to this GRU address, Bellingcat investigators found the names of 305 people. Digging further into this shortlist they discovered Colonel Anatoliy Chepiga, a highly decorated officer in the GRU, and in September 2018 they presented a strong case to identify him as the man claiming to be ‘Ruslan Boshirov’.
In October they identified Dr Alexander Mishkin, a recipient of the Hero of the Russian Federation award in 2014, as the man behind ‘Alexander Petrov’. It also claimed that Mishkin’s honour had been presented to him personally by Vladimir Putin. All this was discovered thanks to passport, phone and driving-licence records that were all freely available on the internet.
“That’s what makes an investigation like this so much fun. The information was out there, but no one had discovered it,” says Higgins. “Because it’s been out there for so long it’s very hard for people to say, ‘Well, you’ve faked this information.’ This is a database from 1999 – how were we able to travel back in time?”
Bellingcat wasn’t finished yet. On Valentine’s Day 2019 the site published a report identifying a third suspect in the poisoning as another high-ranking GRU officer, Denis Vyacheslavovich Sergeev. The site highlighted that the travel itinerary of one Sergey Vyachaeslavovich Fedotov, which it claimed was Sergeev’s alias, matched the locations of a number of international incidents including a visit to Bulgaria in April 2015 at the same time local arms dealer Emilian Gebrev was poisoned.
Next time there’s a big conflict, we’ll make sure the material’s being archived – so from day one, the entire war is being documented”
Higgins believes the revelations to date are just the tip of the iceberg. “The information is out there,” he says. “It is in all these unstructured databases, it’s all a mess, so we’re still digging through tonnes of information and finding new connections. There could be links to other incidents in other countries. It could be that there have been attacks in other countries he’s visited that have been mistaken for pesticide exposure or something. This could be just the start.” The Kremlin has refused to comment on the identities of the three suspects and denies any involvement in the incident, accusing British intelligence of staging the Salisbury attack to stoke anti-Russian hysteria.
For all Bellingcat’s success, the site is just the start of Higgins’s ambitions. He is now working on a searchable database of evidence collected by open-source investigators which would be admissible as evidence in war-crimes cases. “We are developing a way to archive material to make it accessible to future organisations who might need it, like the International Criminal Court,” he says. “So if, in 25 years’ time, evidence is needed in a court case, that evidence will be discoverable through the indexing system.”
Bellingcat has already created a Syrian archive and is soon to open a new office in the Hague which will have a team dedicated to collecting evidence from the war in Yemen. Higgins’s ultimate aim is that all future conflicts will be catalogued in this way. “The idea is that next time there’s a big conflict, we’ll make sure the material’s being archived,” he says. “So from day one, the entire war is being documented. What you start producing from that is all kinds of data about the conflict that otherwise might not be available.”
If his plan is successful Higgins won’t have just belled the cat – he’ll have geotagged it and gathered video and photographic evidence of its criminal activities that will see it held accountable for its actions. And if that works then Higgins believes it will have been worth all the jihadi joke-tagging, Russian trolling and online abuse. “If the work we do is good enough for a court,” he concludes, “then I don’t care about all that other bullshit.”
What the cat dragged in
How Bellingcat and The Insider identified Alexander Mishkin

1. Bellingcat begins with the passport photo of ‘Alexander Petrov’ (above) released by the British police, as well as security camera photos (below) and, later, video footage from the RT interview. The team find no results searching for the name or the passport image, but were able to obtain the passport dossier of ‘Petrov’.

2. As other GRU undercover officers investigated by Bellingcat had retained their forenames, birthdate and place of birth for their aliases – only changing their last name – the team think the same could be true of ‘Alexander Petrov’.
3. ‘Petrov’’s passport dossier references a previous passport, issued in St Petersburg in 1999, so the team search through various leaked databases of St Petersburg residents, vehicle owners and subscribers to telephone services for the forenames (Alexander Yevgeniyevich) and birth date (13th July 1979) listed on the passport details.

As seen on Russia Today interview footage
4. This search results in one exact match: Alexander Yevgenyevich Mishkin, born on 13th July 1979, in a telephone database. Bellingcat finds eight people registered with the same number and address – a communal apartment directly opposite the St Petersburg Military Medical Academy.
5. Presuming that Mishkin graduated from the medical academy to the GRU in Moscow, Bellingcat searches for an ‘Alexander Yevgenyevich Mishkin’ in Moscow, finding a result in an online phone database. A search for this new phone number and Mishkin’s name returns a match in a car insurance database from 2013.

6. A search for the same vehicle in a car insurance database from 2014 revealed that it was registered to Khoroshevskoye Shosse 76B, the address of the GRU’s headquarters (above). The owner had the same birth date and name as the Alexander Mishkin who resided next to the military academy in St Petersburg in 2002.
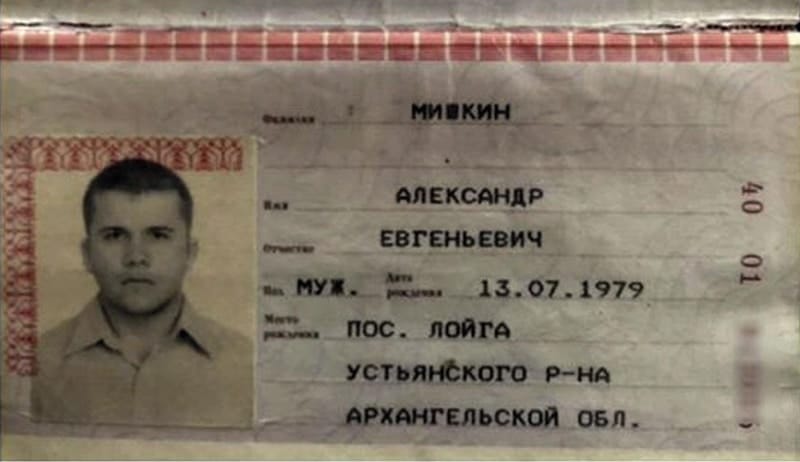
7. Bellingcat obtains a copy of Alexander Mishkin’s scanned passport pages (above). Forensic facial similarity analysis between the passport photo from Mishkin’s passport (dated 2001) and ‘Petrov’’s passport (dated 2016) confirms that the two photographs belong to the same person, having accounted for the 15-year difference between the two.
8. Bellingcat’s Russian investigative partner, The Insider, sends a reporter to the village of Loyga, listed as Mishkin’s birthplace. Here residents recognise ‘Alexander Petrov’ in the photographs released by the British police and in the RT interview as “our local boy” Alexander Mishkin.
9. At least five different residents tell The Insider’s reporter that Alexander Mishkin worked in Moscow “as a military doctor” and had received the Hero of Russia award several years ago. One source told The Insider that Mishkin’s grandmother possesses a photograph in which President Vladimir Putin is shown presenting the Gold Star medal which accompanies the award to Alexander personally, and shaking his hand.
Photos: Getty Images, RT
Slow Journalism in your inbox, plus infographics, offers and more: sign up for the free DG newsletter. Sign me up
Thanks for signing up.